No products in the cart.
👇👇للتوريد تواصل مباشرة مع المشترى
رولمان بلي واويل سيل 1 x قطعه
1327
0
متبقى 1116 يوم
MOUNTING POVIT, SNCB-40, 174391, MFG:FESTO, FOR AIR CYLINDER 2 x قطعه
1000
0
متبقى 1125 يوم
PIPE STAINLESS STEEL 316, 1/2 INCH 5 x متر
1138
0
متبقى 1125 يوم
ونش كهربائي 1 طن 1 x قطعه
1370
0
متبقى 1125 يوم
ترابيزة استانلس بالارطلون 1 x قطعه
1025
0
متبقى 1133 يوم
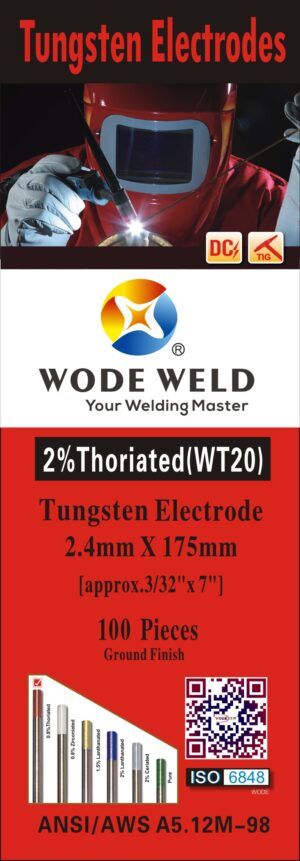
ماكينة لحام صغيره 1 x قطعه
938
0
متبقى 1133 يوم
ماكينة لحام صغيره 1 x قطعه
998
0
متبقى 1133 يوم
ماكينة لحام صغيره 1 x قطعه
935
0
متبقى 1133 يوم
ترولي عدة 1 x قطعه
1048
0
متبقى 1133 يوم
ترولي عدة 1 x قطعه
925
0
متبقى 1133 يوم
أحدث المنتجات

روزته
EGP1.00
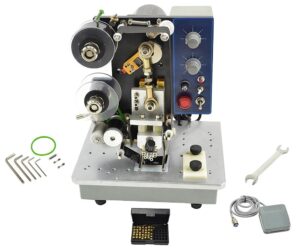
ختامة نصف اوتوماتيك
EGP0.00فرن شرنك صيني
EGP0.00ماكينه الهاند جيت
EGP0.00سير تدريج التمور
EGP0.00خط غسيل البساكت
EGP1.00صنفرة هزاز وسط دونج شونج
EGP0.00صنفرة هزاز كبيرة دونج شونج
EGP0.00صنفرة هزاز وسط دونج شونج
EGP0.00سلم معدني
EGP0.00وحدة شفط و تنقيه الهواء
EGP1.00FIT ديسك خشب الومونيوم
EGP0.00صنيه فديه
EGP0.00كونتاكتور
EGP0.00
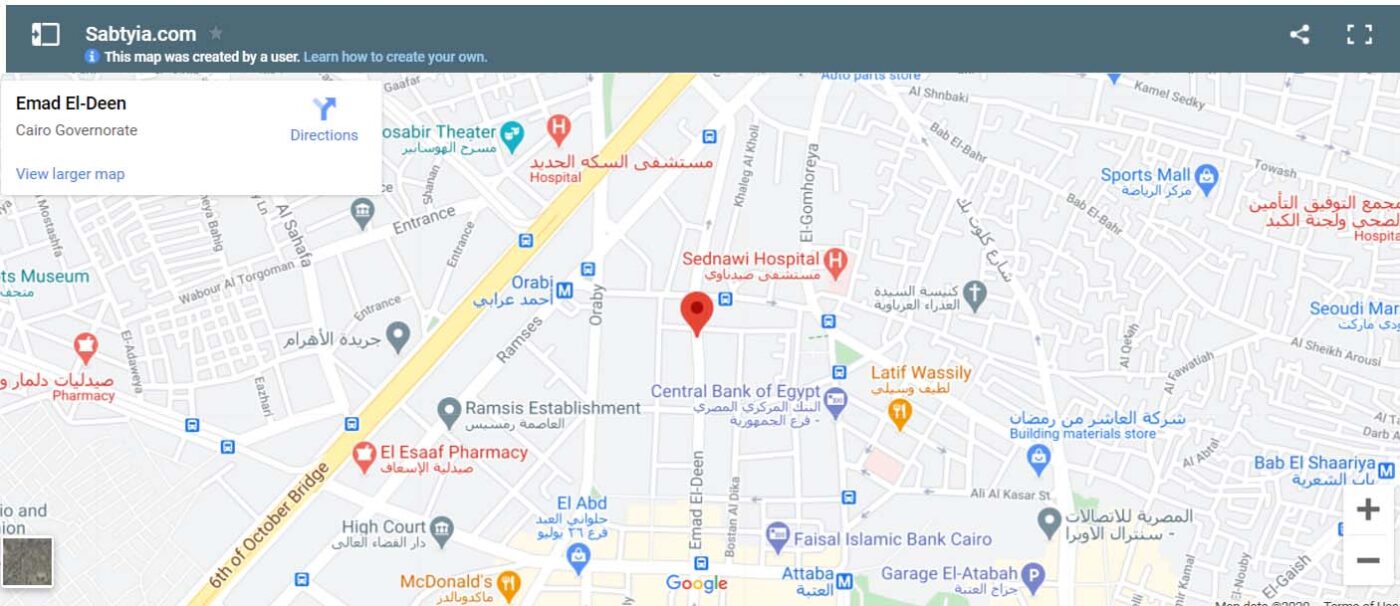
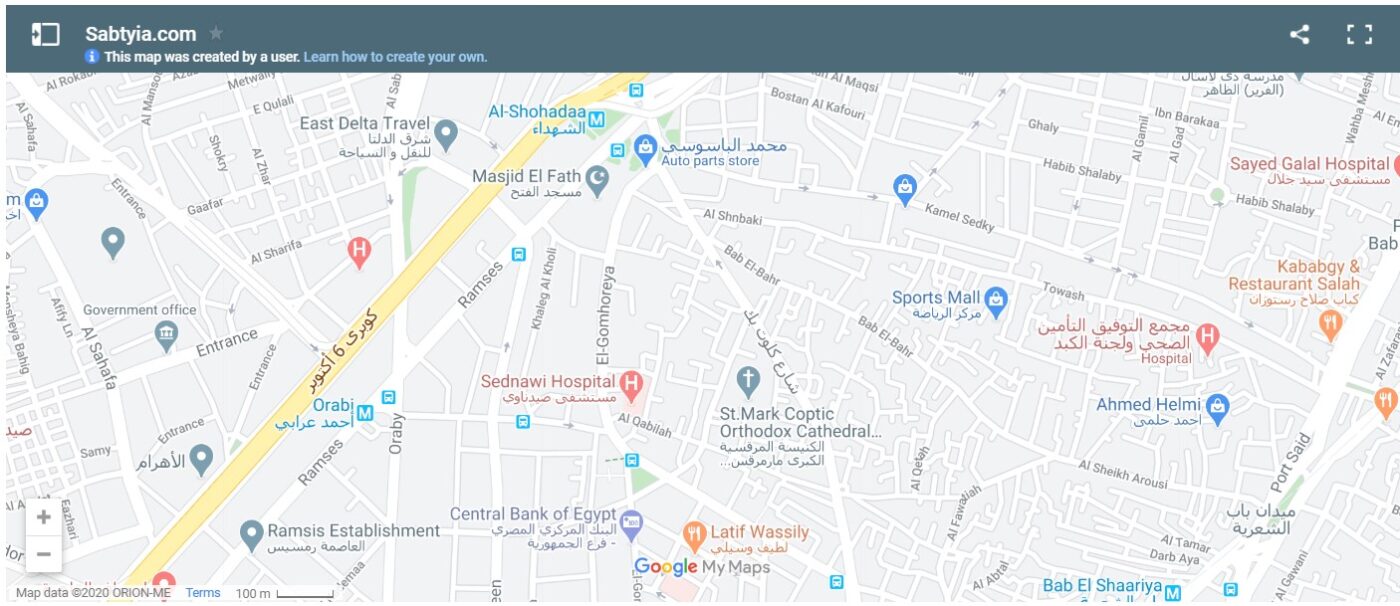
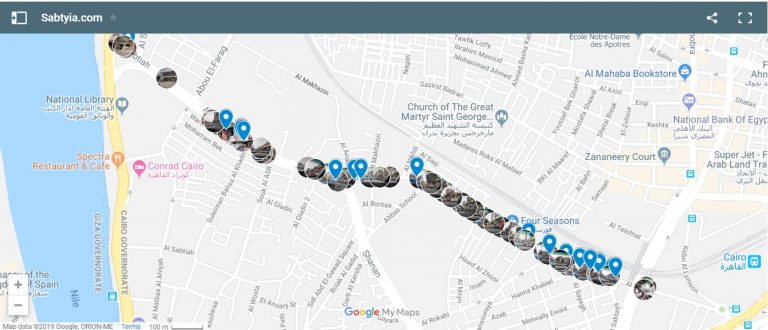
زور محلات وسط البلد وانت فى مكانك
شركاء النجاح



















Previous
Next




















Previous
Next